I have another guest post up at ICTWorks: The Top 10 ICT4D Project Failures Will Surprise You. Click on over to read the list. (This post was edited from originally discussing information security issues.)
Tag: infosec
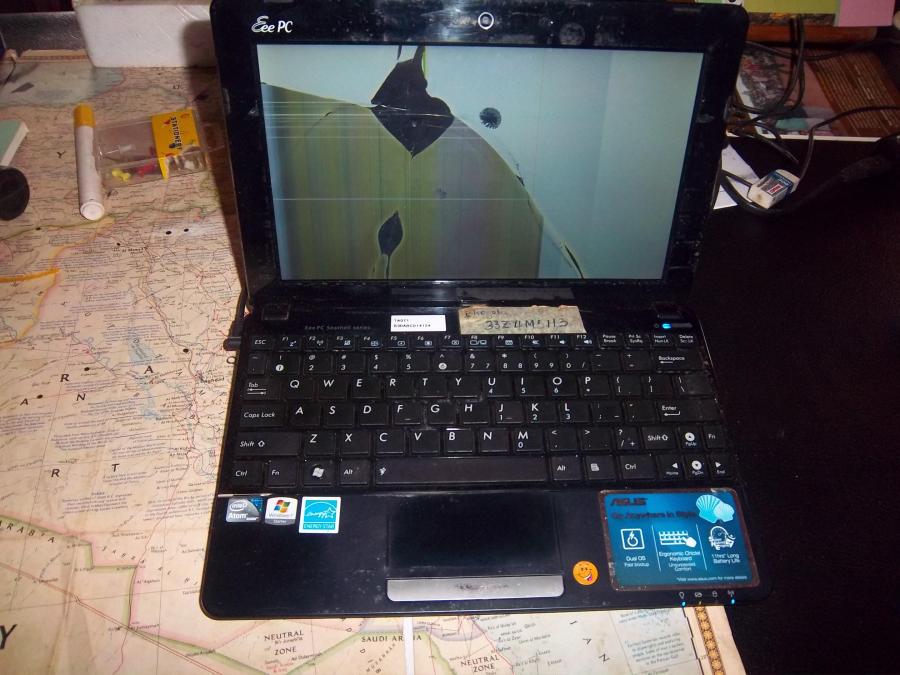
Field Solutions Risk Assessment and Mitigation Strategy
Abstract: In September, 2014, TSC projects lost five laptops and a BGAN in [REDACTED]. It is not always possible to anticipate high-risk projects during the design phase because of changing security circumstances over the life of a project. It is crucial that Field Coordinators and Consultants inform Field Solutions immediately when a laptop or BGAN… Continue reading Field Solutions Risk Assessment and Mitigation Strategy
Country Safety Report
Abstract: Abstract Confidential safety report based upon a trip to visit a conflict zone in October, 2012. This report is not public. It reports background information, documents the security of a variety of specific locations of interest within the country, and makes concrete suggestions for improvements. Media reports had described extremist destruction of communications infrastructure. … Continue reading Country Safety Report
Information Security Protocols v2.2
Abstract: Information security protocols often are too long to be usable. This protocol is a single page with only five key guidelines. It has proven easy to remember and use in real life. Abstract [REDACTED] recognizes that criminals, terrorists, and TLIs 1 may all on occasion threaten the safety, activities, or finances of [REDACTED], its… Continue reading Information Security Protocols v2.2